Successful Security Setup for Model-Driven Apps
Power Apps has empowered us to easily create and build Model-Driven apps. Requiring no heavy coding or experience, you can develop these apps to meet a variety of business needs. And with the recent 2019 release of Dynamics 365 Customer Engagement wave 2, the end-user experience continues to be enhanced with functionality improvements and additions. Building a Model-Driven app is (fairly) simple, but when deploying you must keep security roles and end-user access in mind.
You can choose what users see and access from the 'My Apps' page or Customer Engagement home page by giving app-access to specific security roles. Users will have access to apps based on the security roles they’re assigned to. When deploying, there are multiple potential areas that can affect the user’s ability to access part or all of the app. Below, I’ve provided a comprehensive list of common areas to check if the user can’t see the app or access certain parts of it.
1) Security role is not granted access to the app
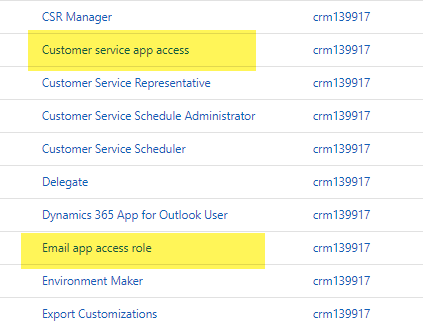
The most common reason a user can’t see or access the app is that the user doesn’t have a security role with access to the model-driven app. Although you can grant any role to any app, this can get messy. If you give a primary security role access to an app, you are giving everybody assigned that role access to the app. In the scenario of deploying multiple apps, you will find yourself in situations where you want to grant access to the app to selected people, and not everyone. This is where the beauty of the app access role design comes into play and lets you easily control access to apps without modifying your primary security roles.
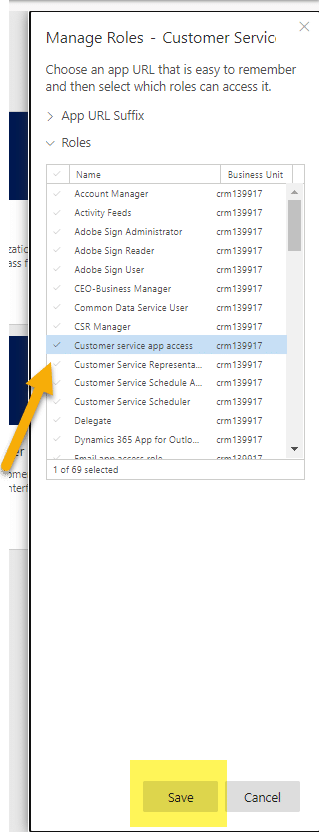
In security roles, you will notice some roles appear in your list that contain “app access”. You can simply add these app access roles to any user to make the app show in up their app list, and you can remove that security role to make their access to the model-driven app disappear.
2) User is missing model-driven app privilege in security role
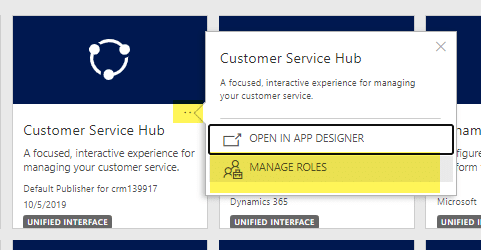
Once your users are assigned the correct security role granting them access to the app they need, you need to make sure that security role is assigned to the Model-Driven app. To do this, navigate to My Apps or Customer Engagement home page and click the ellipses next to the app you’re assigning a security role to. By selecting Manage Roles, a list of all security roles will pop up on the right-hand side. Here is where you select what security roles have access to the selected model-driven app.
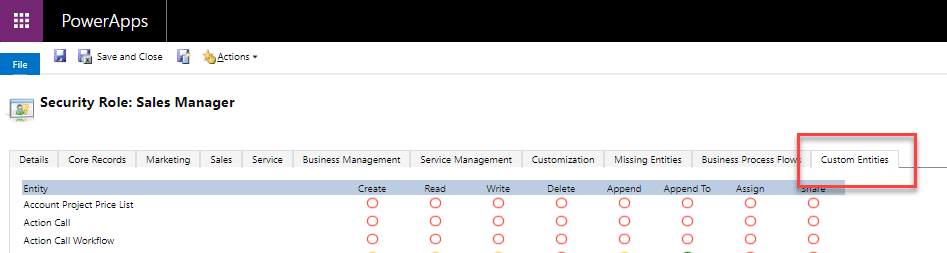
3) Grant access to entities or records in the security role or license
“You do not have sufficient privileges to view this record. Contact your system administrator”. This error message can be frustrating for an end-user, so be sure to add necessary entities that are included in your app when managing security roles- and don’t forget about custom entities. These can be found under the Custom Entities tab for a security role.
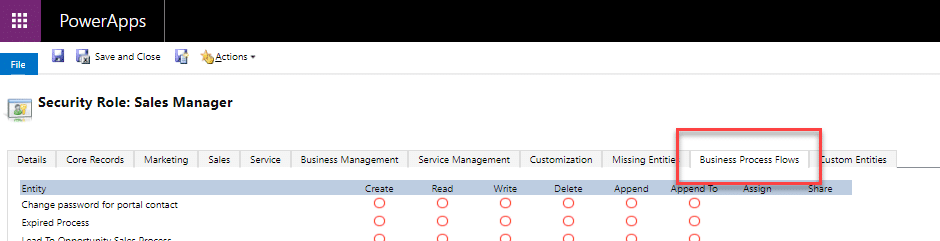
4) Security role needs access to forms, dashboard, and business process flows in the app
When you’re deciding what forms, dashboards, and business process flows will exist in your model-driven app, make sure your users who will be using the app have the correct security set up to have access to them. Business Process Flows are represented as a custom entity and come with their own set of privileges that can be edited within a security role just like any other system or custom entity. You can specify the privileges in the Business Process Flows tab for a security role.
Key Takeaway: Do your due diligence when setting up security for a Model-Driven app. Make sure your users have appropriate privileges in multiple areas. And if you do run into security issues, run through this non-exhaustive list provided.
If you are looking for more information or have more questions about Model-Driven apps, please reach out to us at Stoneridge Software!
Under the terms of this license, you are authorized to share and redistribute the content across various mediums, subject to adherence to the specified conditions: you must provide proper attribution to Stoneridge as the original creator in a manner that does not imply their endorsement of your use, the material is to be utilized solely for non-commercial purposes, and alterations, modifications, or derivative works based on the original material are strictly prohibited.
Responsibility rests with the licensee to ensure that their use of the material does not violate any other rights.