CISA’s Tips On How to Avoid and Respond to Ransomware
A federal agency in the United States has released tips and best practices on how your business can avoid or resolve ransomware attacks.
The Cybersecurity and Infrastructure Security Agency (CISA) recently released a guide on how to avoid these data breaches, which could be devastating to your company's employees and bottom line if you are compromised.
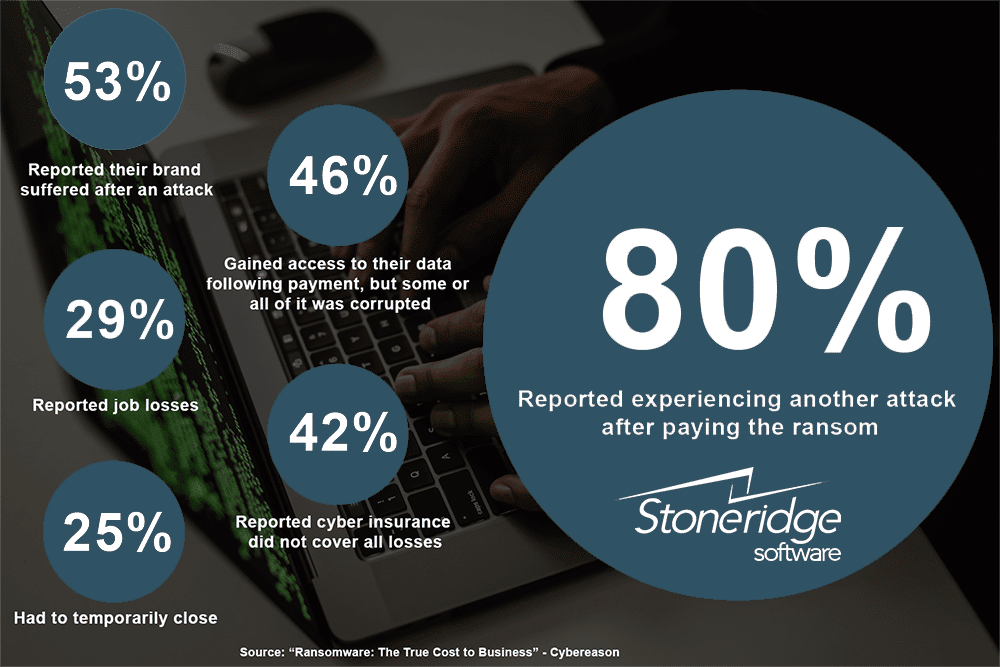
Ransomware attacks are increasing, and many companies that reported paying the ransom either gained access to their data and discovered it was corrupted, or they were targeted with another attack a short time after the first one. The message in those facts is clear: simply paying the ransom is not a solution.
Cybercriminals are becoming more sophisticated in their tactics and are targeting companies of all sizes and employees at all levels. That is why your best solution is to be proactive and have the proper security measures and employee training in place to prevent attacks from happening before they get into your system.
The official CISA recommendations include:
- Maintaining offline, encrypted backups of all data, and regularly testing those backups
- Creating, maintaining, and exercising a basic cyber incident response plan, resiliency plan, and associated communications plan
- Mitigating internet-facing vulnerabilities and misconfigurations by constantly reviewing and updating your system's vulnerabilities and updating software
- Reducing the risk of phishing emails by enabling strong spam filters and implementing a cybersecurity user awareness and training program
- Practicing good cyber hygiene by ensuring your security software is up-to-date and implementing cybersecurity best practices.
The infographic below details findings in a 2021 Cybereason report, which polled just over 1,200 organizations that have been targeted with ransomware attacks and how it affected their companies:
If your company is victimized by hackers, CISA's official recommendation is to not pay the ransom. It says to instead develop a plan of action that:
- Determines which systems were impacted
- Isolates the impacted systems
- Removes and powers down infected devices and triages them for recovery
- Notifies your team members or employees who might be compromised
- Engages with internal and external stakeholders.
Another vital aspect of cybersecurity is remaining calm and following protocols when you think your company might be the target of an attack.
According to SmarterMSP, some ransomware attackers have begun to send out fake attacks before the real ones, with the goal of capitalizing on their target's potential panic, which would lead to straying from protocols and potentially exposing their system even further. This would make it easier for hackers to get in when they launch the real attack.
This stresses the importance of training your employees to not only spot potential threats but also to stay calm and follow protocols if they believe their email or device has been compromised.
Questions?
We are happy to help! Please get in touch with us so we can help you protect your systems.
Under the terms of this license, you are authorized to share and redistribute the content across various mediums, subject to adherence to the specified conditions: you must provide proper attribution to Stoneridge as the original creator in a manner that does not imply their endorsement of your use, the material is to be utilized solely for non-commercial purposes, and alterations, modifications, or derivative works based on the original material are strictly prohibited.
Responsibility rests with the licensee to ensure that their use of the material does not violate any other rights.